
|

|
Building Resilience: CyberNEMO’s Zero Trust Architecture and Risk Roadmap
|
|
December 2025
|
News
Ties with European Cybersecurity projects to accelerate joint innovation
CyberNEMO Presented at CONASENSE Workshop – WPMC 2025
CyberNEMO Featured in AIOTI Report on the EU-Funded IoT and Edge Computing Projects Landscape
|
CHALLENGES & TECHNICAL APPROACH
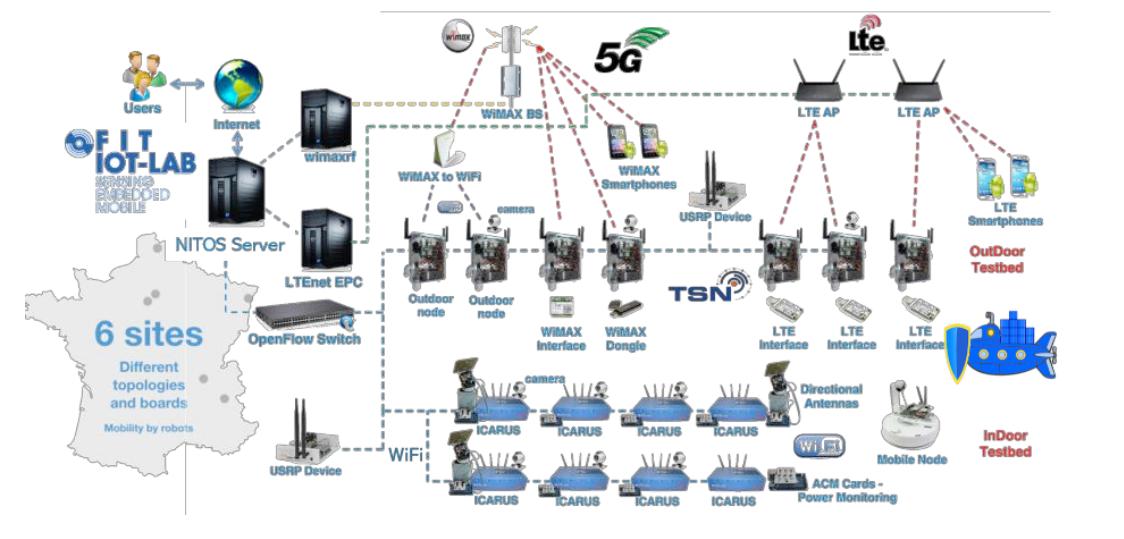
CyberNEMO aims to infuse end-to-end cybersecurity and trust on the IoT-Edge-Cloud-Data Computing Continuum.
CyberNEMO delivers innovations that support resilience, risk preparedness, awareness, detection and mitigation
within Critical Infrastructures deployments and across supply chains on top of NEMO (Next Generation Meta OS – HE 101070118),
which manages the IoT-Edge-Cloud continuum, through an open-source, flexible, adaptable, and multi-technology meta-Operating System.
PROPOSAL
CyberNEMO will offer end-to-end and full stack protection, ranging from a low level Zero-Trust Network Access layer up to a human AI explainable Situation Perception,
Comprehension & Protection (SPCP) framework and tools, collaborative micro-services Auditing, Certification & Accreditation and a pan-European Knowledge Sharing,
risk Assessment, threat Analysis and incidents Mitigation (SAAM) collaborative platform.
|
|
|
Zero Trust Principles in CyberNEMO: Building security by Design
Zero Trust has become one of the most important paradigms in modern cybersecurity. At its core, Zero Trust means no implicit trust; everything must be verified, every time. Every user, device, application, and service must prove its legitimacy before gaining access to resources, regardless of whether it’s inside or outside the corporate network.
What is the Transparent Notary Service (TNS)?
The TNS is essentially a digital notary for network evidence. Its job isn’t to decide whether a piece of evidence is good or bad, but to make sure that once evidence is registered, it stays immutable, timestamped, and cryptographically verifiable.
The TNS uses a lightweight append-only ledger. Each signed statement (such as a configuration attestation, event log, or policy proof) is stored in an immutable data structure like a Merkle tree. This allows anyone to verify inclusion and consistency without having to trust the notary itself.
|
|
Get to know some of our partners…
|
|
|
|
|
Universidad Politécnica de Madrid (UPM)
is one of the most prestigious technical universities in Spain and Europe, renowned for its excellence in engineering, architecture, and technology-related disciplines. Since its establishment in 1971, UPM has grown into a leading institution in higher education, research, and innovation, attracting students from across the globe.
|
Universidad Carlos III de Madrid (UC3M)
The Universidad Carlos III de Madrid (UC3M) is a public and innovative Spanish leading university, which was recognized in 2009 as a Campus of International Excellence in Spain. Founded in 1989, it has more than 25,000 students and more than 2,000 teachers of recognized competence across diverse fields, including Humanities, Science, and Engineering.
|
RWTH Aachen University
is one of the four institutes of the E.ON Energy Research Centers founded in 2006. The institute pursues a multidisciplinary research approach and addresses, among other things, questions regarding the monitoring of active electrical distribution networks as well as the appropriate automation architecture for distributed monitoring and control functions.
|
|
|
Our pilots
|
|
Smart Energy & Smart Water Critical Infrastructures (Italy)
|
The pilot aims to evaluate CyberNEMO solutions in the area of the electricity grid and
the water network.
It involves two use case applications:
- Smart Grid Cybersecurity to protect power networks, substations, and SMs from cyber
threats to ensure reliable electricity generation and consumption.
- Privacy and data breaches in smart grids protecting energy consumption data from
unauthorized access.
|
Secure and Intelligent Media Content Supply Chain Ecosystems (Spain)
|
|
|
The pilot validates end-to-end cybersecurity measures for professional media workflows
spanning contribution, production, and distribution. By integrating zero-trust
approaches with advanced technologies (e.g., ZTNA, ZT-FML, IPDM-DSS), the trial
demonstrates proactive threat mitigation, data protection, and the reliable handling of
multimedia content within a multi-domain, multi-cluster Edge-Cloud environment.
Use case applications:
- Collaborative and Secure Multimedia Content Production involving a media factory
environment where multiple creators and production teams, often geographically
dispersed, collaborate on multimedia assets.
- Efficient and Secure Multimedia Content Distribution Across Multi-Domain Edge-Cloud
addressing the secure delivery of high-quality media content through distributed
content delivery network (CDN) nodes.
|
Proactive & Intelligent Protection of Healthcare Critical Infrastructures (Bulgaria)
|
|
|
The pilot detects and denies unauthorized access and misuse of the sensitive health
records circulating and stored at National Health Information system (NHIS) and National
Health Insurance Fund (NHIF).
Use case applications:
- Detecting and mitigating vulnerabilities protecting patients’ health records, as
well as medical centres’ and hospitals’ data. Risks include exfiltration or
infiltration of sensitive health data, manipulation of data related to medical
logistics, devices, consumables, and financial reports.
- Supply chain collaboration for increased resilience against zero-day vulnerabilities
across healthcare supply chains.
|
Smart Farming and FinTech/Logistics Supply Chain (Greece)
|
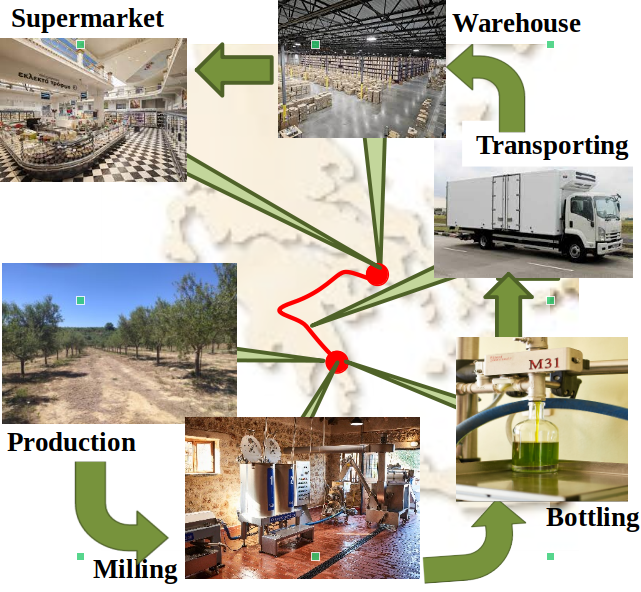
The pilot involves smart agricultural data, retrieved through multiple types of ground
micro-climate/soil/leaf information stations, and logistics-related information to
ensure traceability and auditability ensuring end-to-end cybersecurity.
Use case applications:
- Auditing mechanism to safeguard accountability based on evidence, identify and
verify points of failure affecting product quality.
- Secure and traceable smart F2F trading applying cybersecurity and privacy protecting
federation of (otherwise siloed) IoT platforms, establishing a distributed and
immutable data management to support traceability.
|
Partners involved
|
|

|

|
This project has received funding from the European Union’s Horizon Europe
research and
innovation programme under Grant Agreement No. 101168182
|
|

Copyright (C) 2025 CyberNEMO Project. All rights reserved.
|
|