Understanding the MITRE ATT&CK Framework
In the world of cybersecurity, defenders and hackers are locked in a constant game of cat and mouse. For a long time, defenders focused on who was attacking them (attribution). However, names and locations change. The MITRE ATT&CK® framework shifted the focus to something more permanent: how they attack. ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. Think of it as a comprehensive, living encyclopedia of “bad guy” behavior. It is a globally accessible knowledge base that tracks the specific actions cybercriminals take from the moment they start scouting a target to the moment they steal data or cause damage.
The Anatomy of an Attack
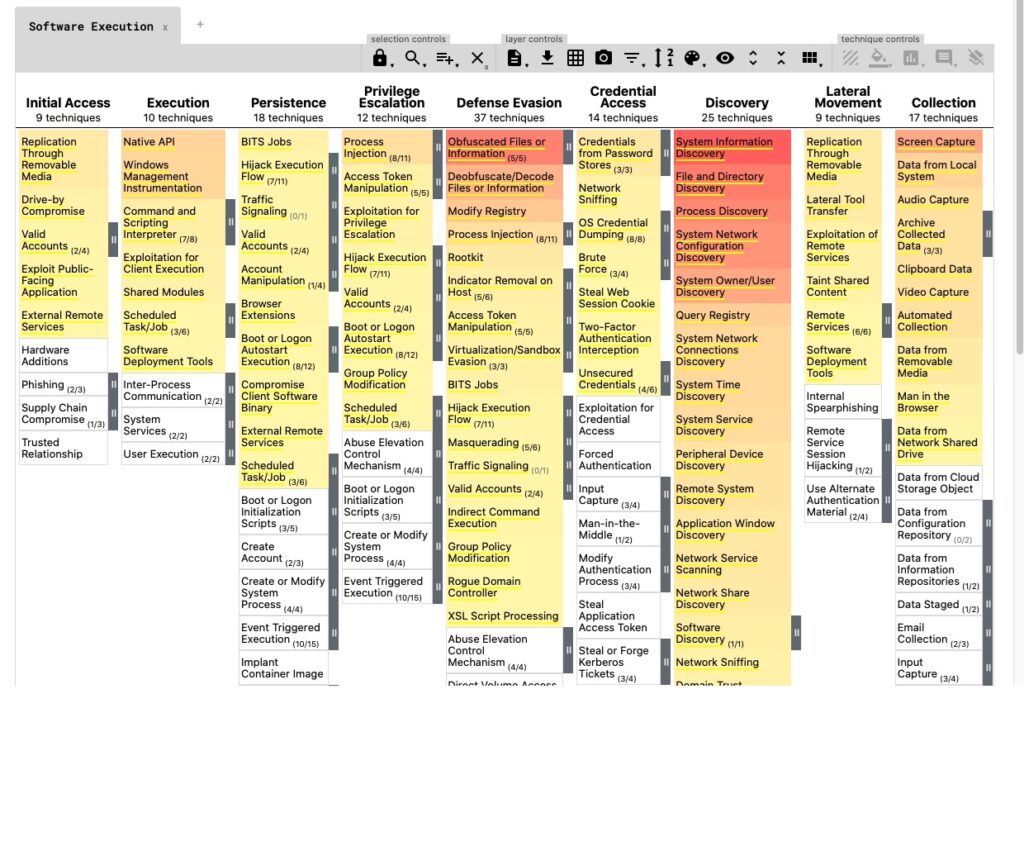
The framework is organized into a matrix that reads like a story of a digital break-in. It breaks down an attack into two main components: (a) Tactics (The “Why”): These are the attacker’s technical goals. For example, a tactic might be “Initial Access” (getting into the network) or “Exfiltration” (taking the data out). (b) Techniques (The “How”): these are the specific methods used to achieve a tactic. If the goal is “Initial Access,” the technique might be a “Phishing” email. By using this common language, security teams across different companies can share information instantly. If a bank in London discovers a new way hackers are bypassing passwords, they can label it with an ATT&CK ID (like T1078), and a hospital in New York will immediately know exactly what to look for.
Mitigations: Building the Shield
The framework isn’t just a list of threats; it’s a roadmap for defense. For every technique listed in the matrix, MITRE provides mitigations, i.e., specific actions organizations can take to prevent a technique from working.
| Tactic | Technique (Example) | Mitigation (Defense action) |
| Initial Access | Phishing | Security awareness training and email filtering. |
| Persistence | Create Account | Use Multi-Factor Authentication (MFA) and monitor new user creation. |
| Exfiltration | Transfer Data to Cloud | Block unauthorized cloud storage sites on the company network. |
Why It Matters
While ATT&CK is a technical tool, its impact reaches everyone. When organizations use this framework, they move away from “guessing” what might happen and start “knowing” what to defend against. It allows companies to test their security systems against real-world scenarios, ensuring that your personal data and the services you rely on—like banking, healthcare, and power—are protected by more than just a firewall and a prayer. MITRE ATT&CK is a resource that has turned cybersecurity from a dark art into a measurable science by documenting the “playbook” of the adversary.

