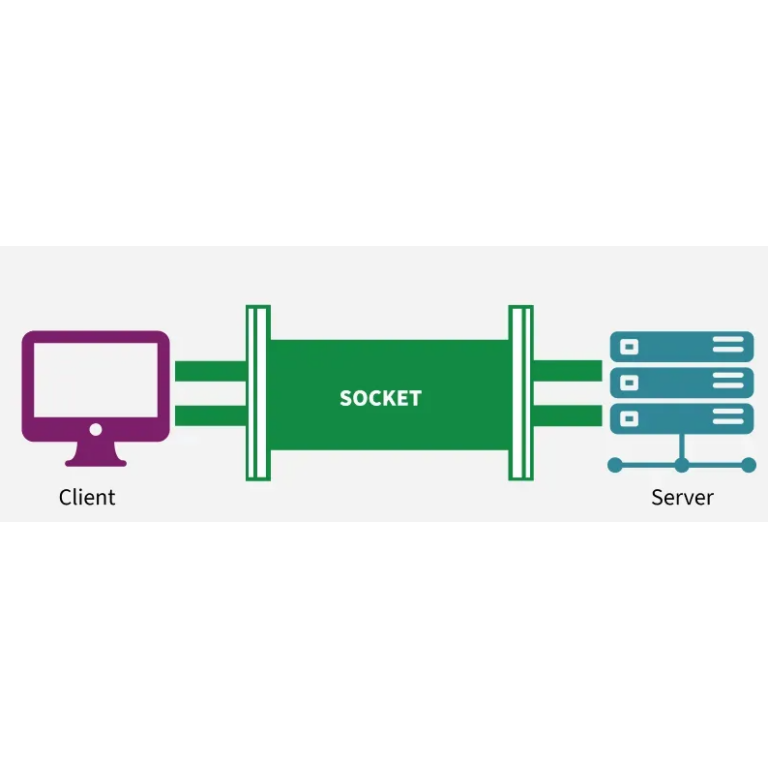
In a standard Kubernetes (K8s) deployment, the sheer level of abstraction is a double-edged sword. While it simplifies orchestration, it often obscures the granular reality of network traffic. For the CyberNEMO project, specifically within WP2, we move past these high-level views to focus on the network socket. Why? Because sockets represent the “ground truth” of connectivity. In a distributed meta-OS, understanding the real-time state of point-to-point communication is the only way to ensure Cybersecurity and Privacy by Design.
Capturing the “Ground Truth” with White Shark
Traditional Kubernetes monitoring often looks at service-level averages, which can mask micro-bursts of latency or intermittent failures. By monitoring at the socket level, our White Shark probe can collect raw, high-fidelity data—including latency, throughput, and jitter—directly from the source. This allows us to see exactly how data moves between specific pods, bypassing the “fog” of virtualized overlays. This level of precision is essential for building a verifiable data plane, ensuring that every packet follows its intended path without manipulation.
Building a Stronger Zero Trust Foundation
Ultimately, focusing on sockets supports the Zero Trust principle of “explicit verification”. In CyberNEMO, we don’t just trust that a connection is secure because it’s inside the cluster. Instead, we use socket-based telemetry to constantly validate that communication patterns match the intended security policies.